Section 1: The Problem
Ransomware is not a niche malware problem anymore. Verizon’s 2025 DBIR found ransomware present in 44% of breaches they reviewed, up from 32% the year before, a 37% increase. (Verizon)
The money is only part of the damage. Even when victims pay, recovery is not guaranteed, and the downtime and rebuild work often dwarf the ransom. Verizon reported the median ransom payment fell to $115,000, but the median is not a comfort if your operations are frozen. (Verizon)
Traditional defenses struggle because ransomware does not need much time to cause irreversible harm. Modern attacks move fast, change constantly, and often blend in with normal activity until encryption begins. Signature matching and “known bad” lists lag behind variants, and human response is slow when alerts arrive too late. (Zapata Sandoval)
Section 2: What Research Shows
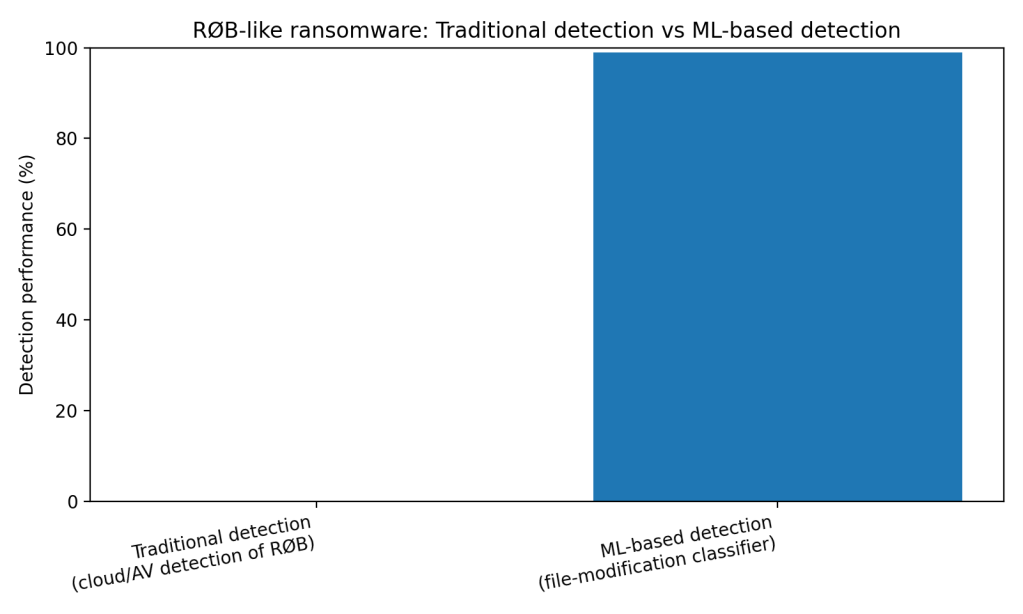
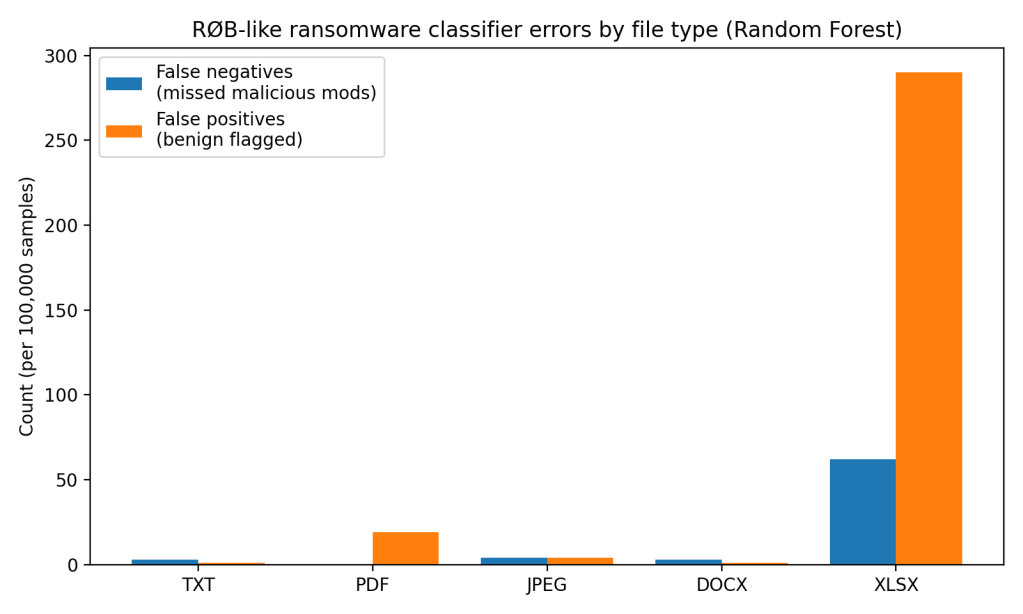
In controlled tests, data-driven detection can spot ransomware behavior with near-perfect accuracy. A clear example comes from a 2023 USENIX Security paper on “Ransomware over Browser” (RØB). The researchers trained simple ML classifiers using features like file entropy change and file size change to identify malicious encryption-like modifications. Their Random Forest model hit about 0.99 accuracy across multiple file types with extremely low error counts in a 100,000 benign and 100,000 malicious modification setup per file type. (Oz)
In the same paper, “traditional” detection did not keep up. The authors tested major cloud storage providers’ built-in ransomware detection and reported none detected RØB during or after the attack. (Oz) That gap, between high lab accuracy and low practical protection, is the core pattern in ransomware defense.
Other pre-encryption approaches report similarly strong retrospective metrics. For example, the RENTAKA framework evaluated multiple classifiers for pre-encryption ransomware detection and reported SVM accuracy of 97.05% with a true positive rate of 0.995 on its dataset. (Zakaria)
Section 3: What the Real World Shows
When detection runs in live workflows, what matters is not “accuracy” in isolation. Timing matters. If you detect after encryption starts, the loss is already real. Pre-encryption or early-stage detection designs aim to stop the write, roll back the process, or isolate the endpoint before widespread encryption. (Kok)
The RØB study is useful because it ties detection directly to an operational outcome. Their first prevention approach hooks browser file system access behavior to prevent permanent malicious modifications before they overwrite user files, then uses classification to decide whether to warn or block. (Oz) Their results show that errors are not theoretical. False positives can appear when benign applications compress or encrypt data, and false negatives appear when attackers use evasion tactics that mimic benign patterns. (Oz)
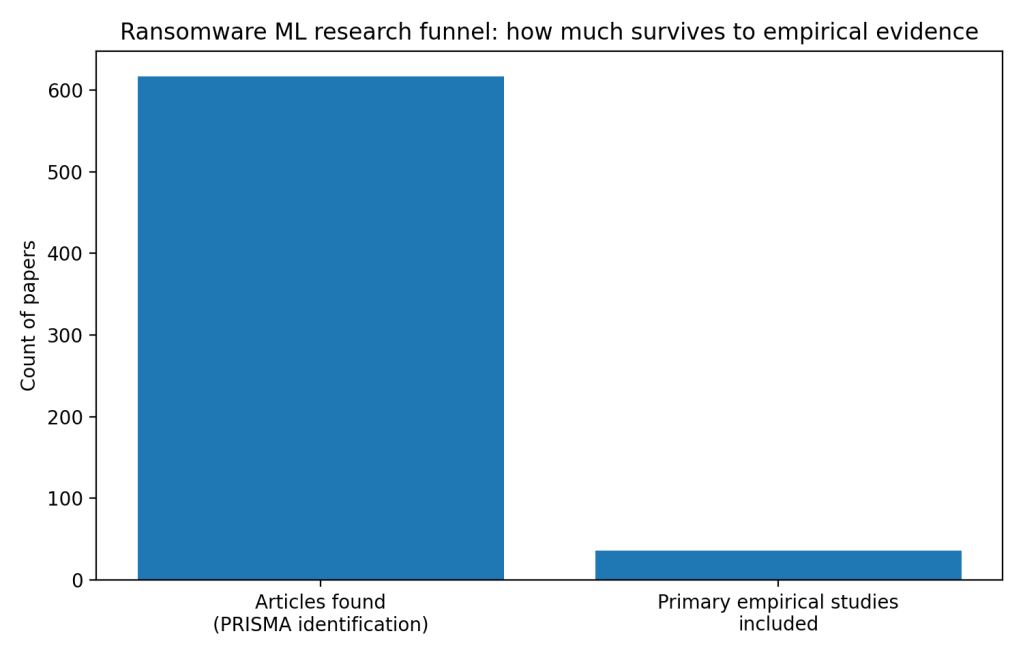
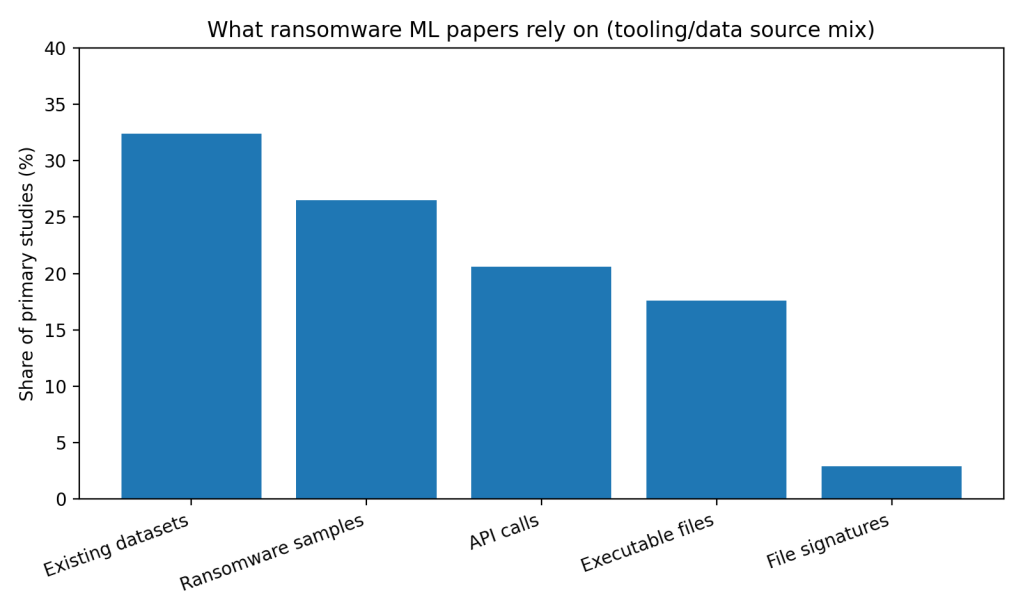
At the broader evidence level, a 2025 PRISMA-based systematic review identified 617 candidate papers and included 36 primary empirical studies. The review also found that “existing datasets” dominate as the most common tool source, and it flags real-time constraints and generalization limits as recurring barriers. (Zapata Sandoval) In other words, the literature is large, but a smaller slice survives into empirical work that looks like the conditions defenders face. (Zapata Sandoval)
Section 4: The Implementation Gap
The first barrier is workflow cost. Security teams already drown in alerts, and ransomware defenses that introduce extra prompts, extra endpoints, or frequent user interruptions do not survive contact with real operations. The RØB authors explicitly note that benign apps doing heavy compression or encryption can trigger false positives, and mitigating that often means more user prompts, which increases friction. (Oz)
The second barrier is attacker adaptation. The RØB paper shows evasion is not hypothetical. By combining data padding and partial encryption to mimic benign changes, the attackers could evade the classifier, creating hundreds of false negatives in the authors’ adaptive evaluation. (Oz) Defenders do not deploy tools they expect to degrade quickly unless they have a strong update pipeline and clear operational value.
The third barrier is data realism. The 2025 PRISMA review shows a heavy dependence on “existing datasets” as the dominant tooling source in the literature, at about 32.4% of the tool mix it summarizes. (Zapata Sandoval) Existing datasets are safer and easier, but they often miss the messiness of enterprise environments, including mixed workloads, noisy endpoints, and policy constraints. (Zapata Sandoval)
The fourth barrier is performance and latency. The same review highlights that computational requirements and analysis duration can be insufficient for real-time detection, especially when models rely on heavyweight features. (Zapata Sandoval) In ransomware, “late but accurate” is a losing trade.
Section 5: Where It Actually Works
Ransomware detection tends to work better when it is paired with a hard control. The RØB paper’s most practical idea is not “better classification.” It is interception, preventing permanent modification, then using detection to decide when to block or warn. That turns the model from a dashboard into a stop button. (Oz)
It also works better when the signal is cheap and local. Features like entropy change and file size change are fast to compute and easy to attach to a file-write pipeline. That helps keep detection inside the time window that matters. (Oz)
Section 6: The Opportunity
Ransomware defense has strong research results, but adoption lags because teams need low-friction, early, and enforceable interventions, not another alert stream. (Zapata Sandoval)
Takeaways you can act on
- Tie ML detection to automatic containment, stop writes, isolate endpoint, kill process, not “notify and wait.” (Oz)
- Budget for false positives in the UI and workflow, route them through tiered thresholds instead of binary alarms. (Oz)
- Train and test on signals collected in realistic environments, not only static “existing datasets,” and publish those datasets when possible. (Zapata Sandoval)
- Measure time-to-intervention as a primary metric, not only AUROC or accuracy. (Zapata Sandoval)
- Build an update loop for evasion, treat detection models like continuously patched software. (Oz)
References
[1] Oz, et al. “RØB: Ransomware over Browser.” USENIX Security Symposium, 2023.
[2] Verizon. “2025 Data Breach Investigations Report, Executive Summary.” 2025.
[3] Zapata Sandoval, Jonathan Ismael, et al. “Ransomware Detection with Machine Learning: Techniques, Challenges, and Future Directions, A Systematic Review.” Journal of Internet Services and Information Security, vol. 15, no. 1, 2025, pp. 271–287. DOI: 10.58346/JISIS.2025.I1.017.
[4] Albshaier, Latifa, et al. “Earlier Decision on Detection of Ransomware Identification: A Comprehensive Systematic Literature Review.” Information, vol. 15, no. 8, 2024, article 484. DOI: 10.3390/info15080484.
[5] Kok, S. H., et al. “Early Detection of Crypto-Ransomware Using Pre-Encryption Detection Algorithm.” Journal of King Saud University, Computer and Information Sciences, vol. 34, 2022, pp. 1984–1999. DOI: 10.1016/j.jksuci.2020.06.012.
[6] Zakaria, W. Z., et al. “RENTAKA: A Novel Machine Learning Framework for Crypto-Ransomware Pre-Encryption Detection.” International Journal of Advanced Computer Science and Applications, vol. 13, no. 5, 2022. DOI: 10.14569/IJACSA.2022.0130545.
[7] FBI. “FBI Releases Annual Internet Crime Report.” Press release, Apr. 23, 2025.
Leave a comment